Safe browsing tips
A few tips and tricks to help you online
Confirm the address before signing in
Before signing in to a website, you should double check the website address in your browser. Sometimes scammers will use a similar looking website in an attempt to steal your login details.
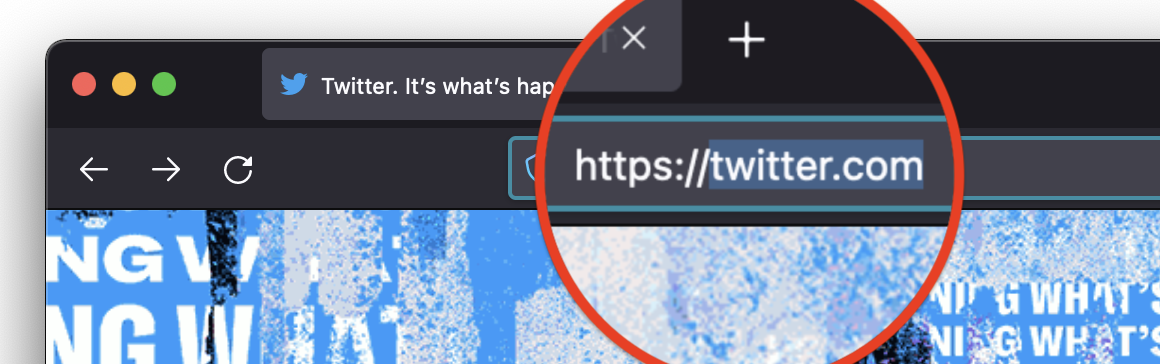
Click on the address bar at the top of your browser, and make sure it’s both secure (look for https) and the correct address (in this example, twitter.com is spelt correctly).
Apply Software Updates Regularly
Because software bugs happen all–the–time.
A lot of the time, software bugs are just annoying (like when a button doesn’t work).
But sometimes, software bugs are security related and used by scammers and cyber criminals to get access to your device, steal your data or take over your accounts.
It’s generally advised to keep your Operating System, Web Browser, and other software regularly updated, because software updates can include fixes for security issues.

Review installed Browser Extensions
Web Browser add-ons and extensions can improve the overall features and experience you have when browsing the web.
On the flip side, you might be giving them permissions to read and alter your website requests and data.
We suggest you regularly review the browser add-ons / extensions you have installed, and make sure you trust the developer that wrote the software.
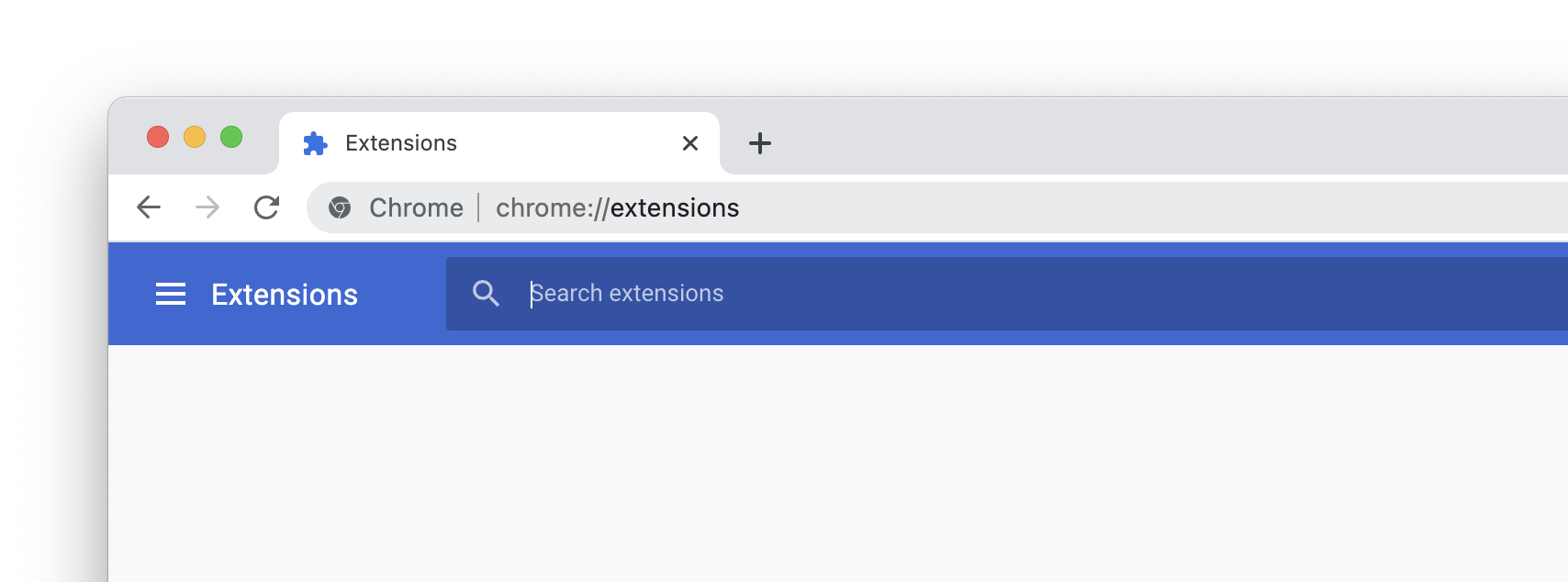
Helpful links
- Manage extensions on Google Chrome
- Manage extensions on Mozilla Firefox
- Manage extensions on Apple Safari
- Manage extensions on Microsoft Edge
Use two-factor authentication
Also known as “2FA”, two-factor authentication adds an extra layer of security to the typical Login process. It requires you to enter a unique code, in addition to your Login details.
These codes are often sent by SMS, but you can choose to use an Authenticator app instead. This makes them portable, and (arguably) more secure than receiving them over SMS.
Where possible, we suggest enabling two-factor authentication on your accounts.
Using private browser windows
Most modern browsers offer an incognito or private mode of browsing, which aims to reduce the footprint left on the computer.
According to Firefox, private browsing “does not save your browsing information, such as history and cookies, and leaves no trace after you end the session”
- Apple – Using Private Browsing in Safari
- Google – How to browse Chrome in private
- Microsoft – Browse InPrivate in Microsoft Edge
- Mozilla – Private Browsing in Firefox
Guest Mode
Some web browsers, such as Google Chrome, offer a “guest mode” profile so that “when you exit Guest mode, your browsing activity is deleted from the computer”.
This could be particularly useful when you’re borrowing (or lending) your computer, or using a public machine.
It’s not perfect
Although these features may reduce risk on the computer itself, they don’t make you anonymous on the Internet. Mozilla has an article about the common myths about private browsing.
Other resources
Here are a few resources from around the Internet:
- Mozilla - How to stay safe online
- Google - Tools and tips to help you stay safe online
- eSafety Commissioner - Back at school? 6 online safety tips for the 'new normal'
The Australian Government publish various resources on the Australian Cyber Security Centre website:
- ACSC - Information for Individuals and Families
- ACSC - Easy steps to secure your devices and accounts
- ACSC - Step by step guides
The UK National Cyber Security Centre also publish various resources: